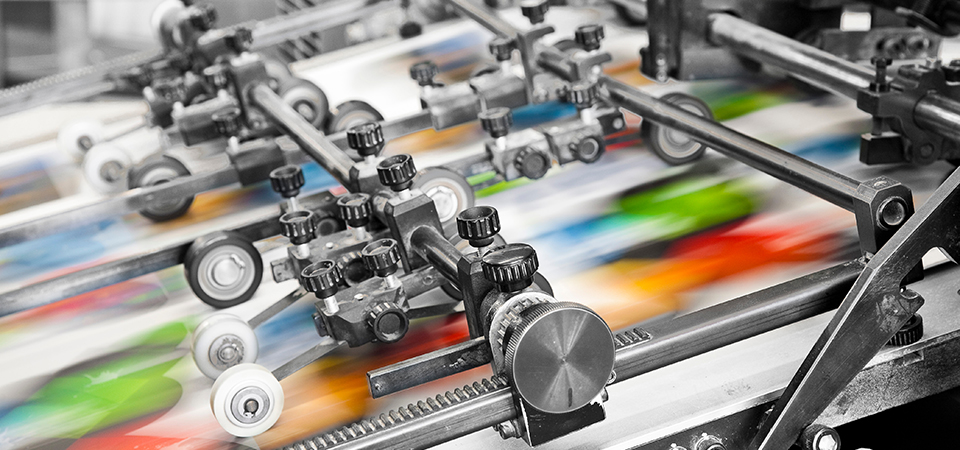
Office Equipment
It’s a digital world, but that doesn’t rule out the need for physical documentation. As experts in business connectivity, we have optimized printer or copier equipment plus full-service solutions for you.
- Small Office Copiers & Printers
- Freestanding Office Copiers & Printers
- Production Printers
- Offline Finishing Solutions
- Wide-Format Printers
- Envelope Printers
- Copier & Printer Sales or Leasing Options
- Copier and Printer Maintenance
- Document Management
IT Services
We make connecting simple, reliable and secure. Discover how CEI can help you empower your business with your right-fit IT solution that delivers worry-free business operations.
- Managed IT Solutions
- Hybrid Office Solutions
- Backup & Disaster Recovery Solutions
- Cloud Server Solutions
- Server Solutions
- Network Security Solutions
- Business Communications & VOIP Solutions
- Multi-Tiered Levels of Support Services
- Infrastructure Services